Microsoft BitLocker – YellowKey zero-day exploit

There's nothing more dangerous than a bored engineer with a screwdriver, and hell hath no fury like a security researcher scorned. Last month, Security researcher Chaotic Eclipse (aka Nightmare-Eclipse) published two zero-day exploits, BlueHammer and RedSun, that made Windows Defender offer up system administrator privileges. They did this after their disclosure reports were allegedly dismissed by Microsoft's security team, resulting in a vendetta of sorts. Eclipse has now done it again, posting two new zero-day exploits, the first one an extremely serious BitLocker exploit named Yellow Key that grants full access to a locked drive. The second one, GreenPlasma, doesn't have a complete proof-of-concept (PoC), but it allegedly performs a local privilege escalation and gains system-level access. Given Eclipse's track record, it's a fair bet that it works as advertised.
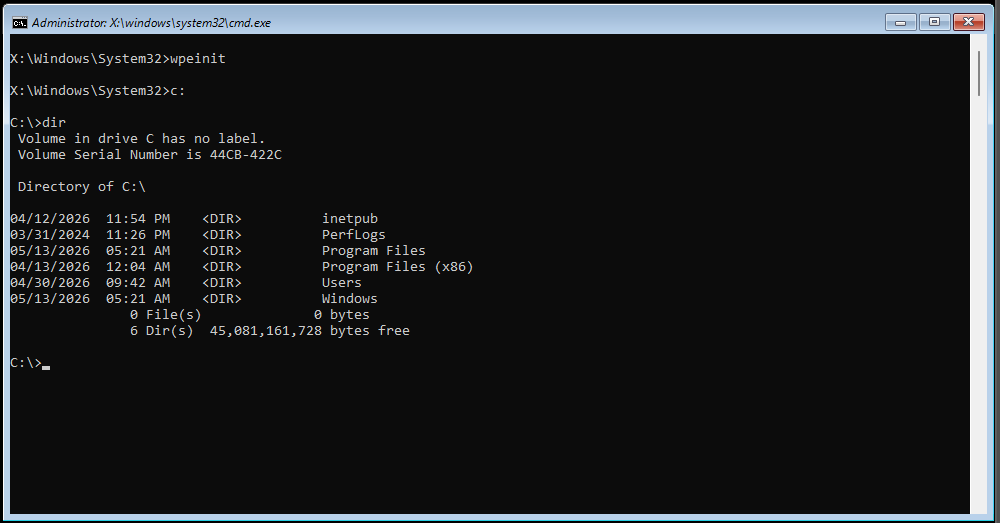
YellowKey can be triggered simply by merely copying some files to a USB stick and rebooting to the Windows Recovery Environment. We tested this ourselves, and sure enough, not only does it work, it bears all the hallmarks of a backdoor, down to the exploit's files disappearing from the USB stick after it's used once.
Latest Videos From
To say that this is dangerous is an understatement. Not only is it an immediate concern as BitLocker cannot be trusted for encrypting drives, but the way the exploit executes and its files disappear also raises very uncomfortable corporate and/or political questions. YellowKey also reportedly works in Windows Server 2022 and 2025, but not in Windows 10.
BitLocker protects millions of machines worldwide across home, enterprises, and governments, especially as it's enabled by default in Windows 11. As far as we can tell, a drive can't be taken from machine Alice and opened in machine Bob because the encryption keys are in Alice's TPM, but it's not hard to just up and steal a laptop, mini-PC, or even desktop.
Eclipse notes that using a full TPM-and-PIN setup doesn't help, as apparently, they have a variant for that scenario that they haven't published a PoC for. They also state the vulnerability is well-hidden, and that they "could have made some insane cash selling this, but no amount of money will stand between me and my determination against Microsoft."
As for GreenPlasma, it's supposed to get an attacker full system-level access (even higher than administrator) by manipulating the CTFMon process into placing a crafted memory section object — a slice of memory that can be shared between processes or mapped to a file — in any Windows' Object Manager section the SYSTEM user has write access to, bypassing regular access controls.
Stay On the Cutting Edge: Get the Tom's Hardware NewsletterFrom thereon, the exploit code can get access to regions of memory they're not meant to and leverage that for any number of shenanigans, the most obvious one being getting full system access. This is bad enough for a desktop system, as any program can get full access, but it's particularly bad for server environments, where any regular user can get control of the server and, by extension, everyone else's data.
Meanwhile, as of this writing, there is no official response from the company about YellowKey or GreenPlasma. BlueHammer has already been patched, and Chaotic claims that Microsoft silently patched RedSun, but there's no official word on that either.

Follow Tom's Hardware on Google News, or add us as a preferred source, to get our latest news, analysis, & reviews in your feeds.
See all comments (30)
Bruno Ferreira is a contributing writer for Tom's Hardware. He has decades of experience with PC hardware and assorted sundries, alongside a career as a developer. He's obsessed with detail and has a tendency to ramble on the topics he loves. When not doing that, he's usually playing games, or at live music shows and festivals.
30 Comments Comment from the forums-
Apple exploit incoming.
Just the other day it was Linux, now its Microsoft. Android probably coming soon too.
Its all a cycle. Someone is next. Nobody is perfect. Reply - Yes, at first it seems like the company hasn't done enough, whatever company has been hacked or exploit found. But it seems EVERYTHING is being hacked these days. Personally, I've received nearly a dozen notices saying my info has been stolen and have had free identity protection services for over ten years now. Safe to say everyone's critical personal info is in some black market by now. Reply
-
You're telling me the most relevant reason of why Microsoft forced everyone to have (enabled) TPM in order to install and use Win11 is a hackable joke? SAY IT AINT SO!
surprisedpikachuface.jpg
Regards. Reply - Do I understand this correctly that portable drives protected by Bitlocker to Go are still secure? And are drives protected where the key is NOT stored in TPM, e.g. the key is stored in a text file somewhere away from the locked computer, are those still secure? Reply
-
They did this after their disclosure reports were allegedly dismissed by Microsoft's security team
Sounds about right, maybe they should name and shame the one who dismissed the disclosure. Reply - SOS, DD it's Microsucks. What did you expect? :anguished: Reply
-
TechieTwo said:SOS, DD it's Microsucks. What did you expect? :anguished:
yawn... Reply -
TechieTwo said:SOS, DD it's Microsucks. What did you expect? :anguished:
And yesterday it was Apple, and last week it was Linux.
Your point? Reply -
-Fran- said:You're telling me the most relevant reason of why Microsoft forced everyone to have (enabled) TPM in order to install and use Win11
You know that actually is a really good point Fran.
We all know the TPM security propaganda since the Windows 11 launch. However why are TPM chips necessary in practice if they don't actually secure? Reply -
ezst036 said:You know that actually is a really good point Fran.
They are not necessary. That is the grift.
We all know the TPM security propaganda since the Windows 11 launch. However why are TPM chips necessary in practice if they don't actually secure?
Encryption (reliable even) has existed for ages in different ways and shapes before TPM was designed and implemented. It's a nice to have, for sure, but make it mandatory? Nah.
Marrying your hardware to a physical encryption tool does not make it inheritely more secure. That's just gaslighting: "it's ok, this is totally to make your stuff more secure! pinky promise!". It's been widely reported that MS doesn't even use anything with TPM unless you actively enable BitLocker or anything else that requires encryption and supports TPM.
But oh well... TPM is not a bad thing, just to be clear. Microsoft forcing people to have it for an OS upgrade is the bad thing.
Regards. Reply
Схожі новини
Saudi warplanes struck militias in Iraq during war, sources say

'US, China should be partners not rivals': Key takeaways from Trump and Xi's much-watched summit

ППО ліквідувала 652 з 675 БпЛА та 41 ракету, зафіксовано влучання 15 ракет та 23 ударних БпЛА на 24 локаціях – Повітряні сили

